Introduction:
In a recent project, I encountered a challenging issue while deploying an operating system using a custom Task Sequence in MCM (Microsoft Configuration Manager). Everything seemed to be going smoothly until I encountered an error in the middle of the deployment process. This post aims to share my experience and the solution I found to address the problem.
Problem Description:
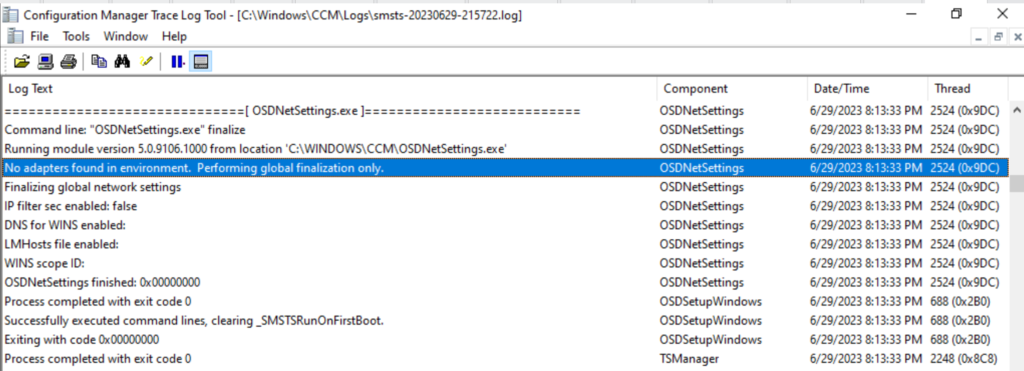
During the deployment, after successfully applying the Windows 10 operating system and restarting WinPE (Windows Preinstallation Environment), I faced an error specifically related to the “Install Application” step. Upon investigating the SMSTS.log, I discovered an error message indicating “No adapters found in environment.” However, I knew that the correct NIC (Network Interface Card) adapter with the appropriate driver was present.
Investigation and Resolution:
To troubleshoot further, I ran the command “ipconfig /all” in the Command Prompt (CMD) to check the IP configuration. Unfortunately, I noticed that the static IP address was missing. As a result, the client machine couldn’t establish a connection with the Active Directory and the Management Point, leading to failures in domain joining and application installation.
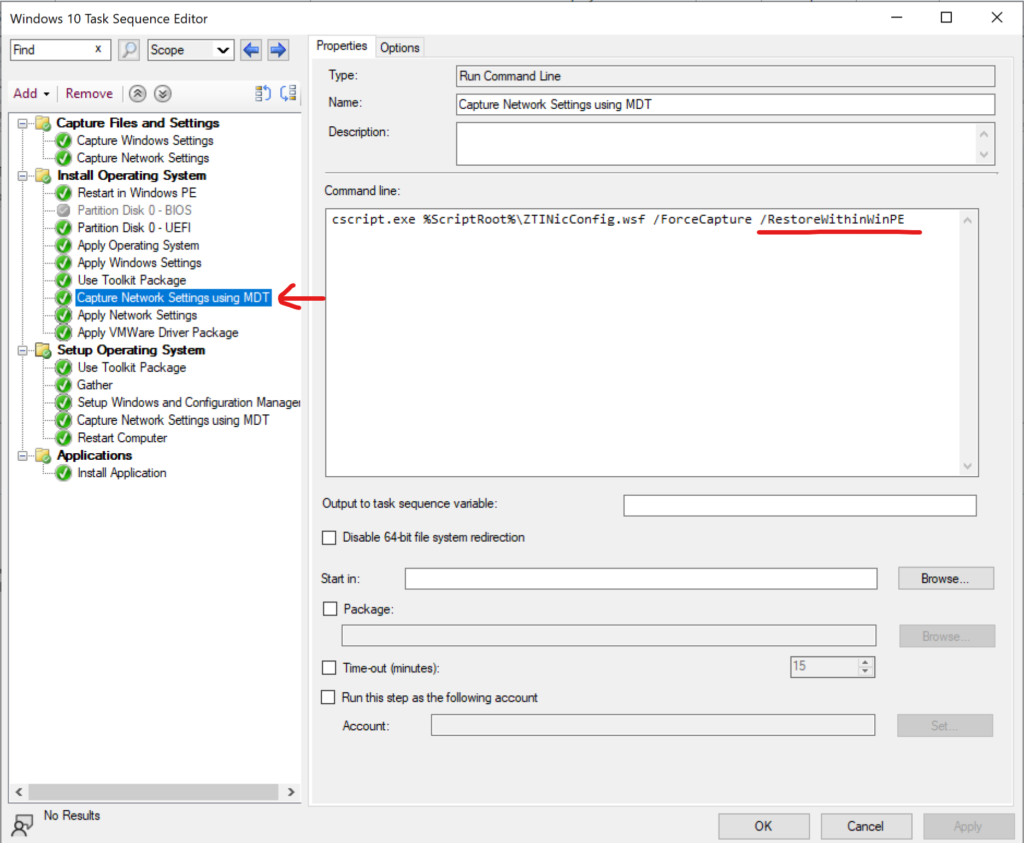
To address this issue, I decided to include the MDT (Microsoft Deployment Toolkit) toolkit package in the Task Sequence. I utilized the “Capture Network Setting Using MDT” step, which allowed me to capture and store the static IP configurations. These settings could then be reused whenever needed. It’s important to note that when using this step, it is crucial to include the “/RestoreWithinWinPE” switch to ensure successful execution.
Successful Completion:
Implementing the MDT toolkit package and incorporating the “Capture Network Setting Using MDT” step in both the “Install Operating System” (WinPE) and “Setup Operating System” (post-install) processes proved to be the solution. With the static IP configurations captured and restored appropriately, the Task Sequence was able to complete successfully.
Conclusion:
In the world of operating system deployment, unexpected errors can occur at any stage. It is essential to analyze log files, perform thorough investigations, and employ appropriate troubleshooting techniques. In this case, the use of the MDT toolkit and the “Capture Network Setting Using MDT” step resolved the issue and ensured a successful deployment.